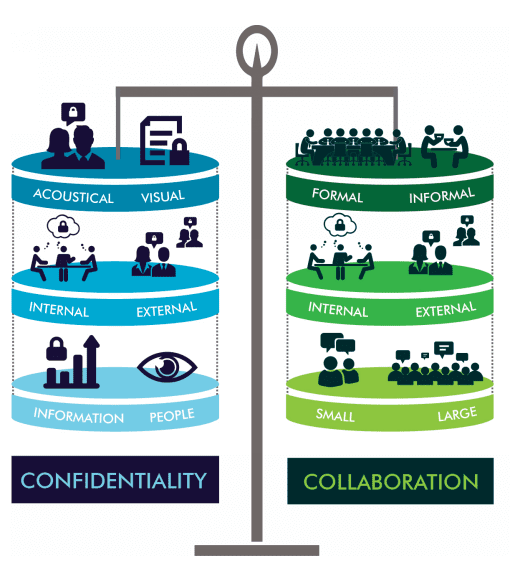
Balancing Confidentiality with Collaboration
When first considering the tenets of a “secure” building it’s easy to imagine a heavily-guarded facility filled with an array of retina scanners, guard dogs, and pressure-sensitive tiles à la Mission Impossible. But then again, it’s hard to create a visual manifestation of things like intellectual property (IP), copyrights, trademarks, etc.
As many nations with a strong service sector find that intellectual property value is increasing year-after-year, a recent report from the World Intellectual Property Organization may shed some light as to why the manufacturing sector is also feeling the increased value of IP. In it, the report states, "that intangible capital – in the form of technology, design and brand value as well as workers’ skills and managerial know-how – has become critically important in dynamically competitive markets." The report goes on to illustrate how such non-tangible capital (also including R&D, and after-sales services) are contributing significantly more to a product's value than in previous years.
It therefore should come as no surprise that analysts are predicting that global cybersecurity spending will exceed $1 trillion by 2021. In conjunction with this, the importance of other, more traditional types of security and privacy measures are also on the rise—especially in the workplace.
Competing against this recognition of the importance of information security is the increasing pressure to create room for collaboration. Private offices are nearly a thing of the past as organizations recognize the need for teamwork and workplace flexibility. With over 81% of North American offices having converted to an open-space floor plan, it might seem like these two forces are en route to an eventual clash.
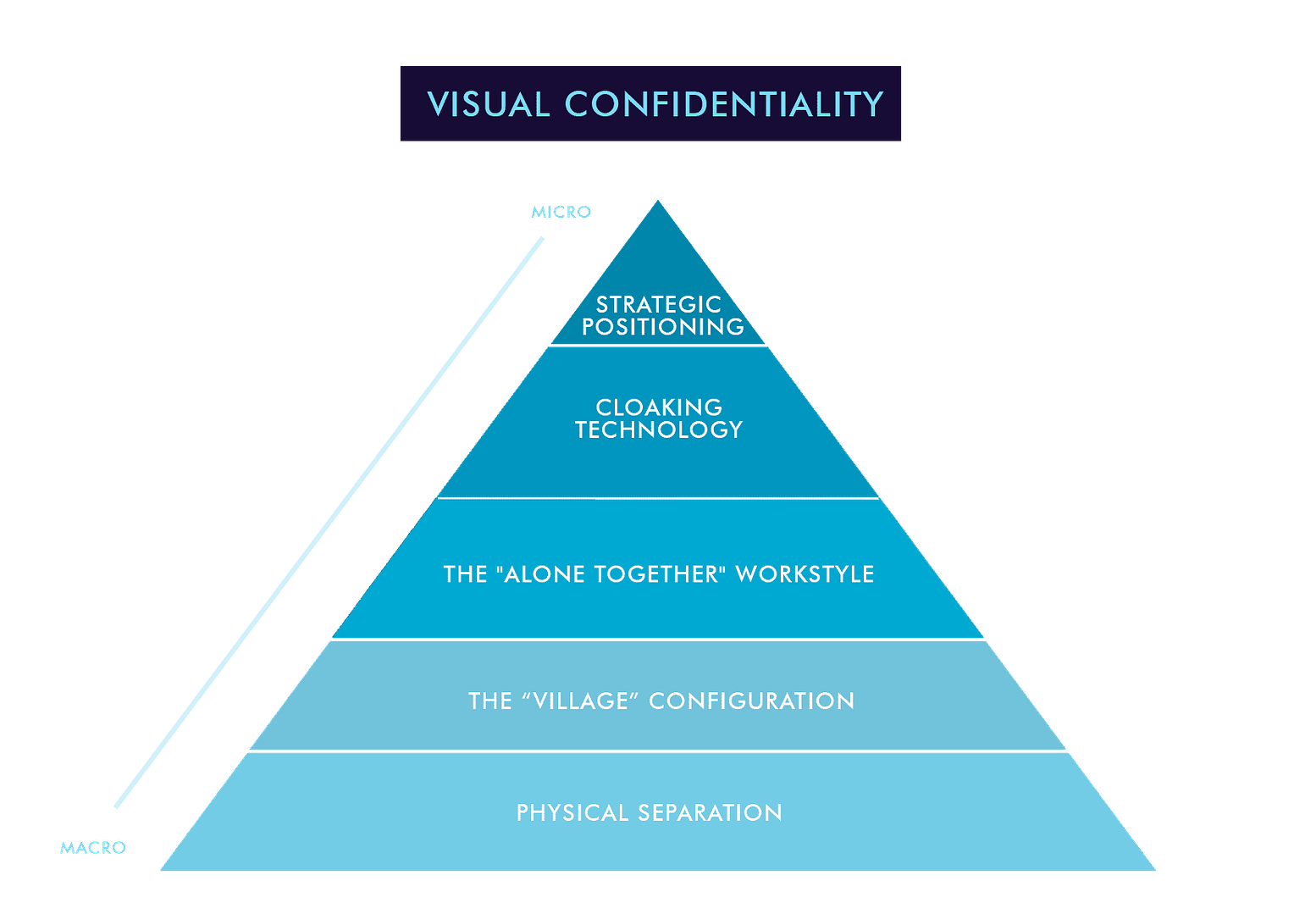
Organizations that work with IA Interior Architects are especially aware of these competing forces. As we continue to design workspaces for financial technology, software, banking, legal, automotive, and other organizations that see significant value in protecting their (or their clients’) information, it becomes necessary for us at IA to make sure that the lessons learned, successes, and methodologies that enable us to create secure spaces get shared among our global network of architects and designers so that we maintain our position at the leading edge of designing with confidentiality in mind. Our methodology centers around the identification of six core steps to creating visual confidentiality in an open or semi-open work environment (see figure 1) and ensuring that we are consistently mindful of the collaborative needs of our clients. In this post, we focus on one of those principles of confidentiality–the visual.
Physical Separation
During the development process of workplace strategies, IA strategists are careful to note any and all traffic patterns, needs, space requirements, and unnecessary overlap. As we acquaint ourselves with our clients and their existing working arrangement, the first step in designing for confidentiality is to mitigate any unnecessary security risks using physical separation.
During this process, we identify differing access requirements, “tour paths,” and establish complimentary physical boundaries to limit unnecessary access without overly constricting collaboration. In addition, this step helps to identify potential locations for necessary meeting points, where users with similar security requirements can have easy access to each other while making it less likely for those without access rights to enter the space (such spaces are described in greater detail in the “Alone Together” Workstyle section).
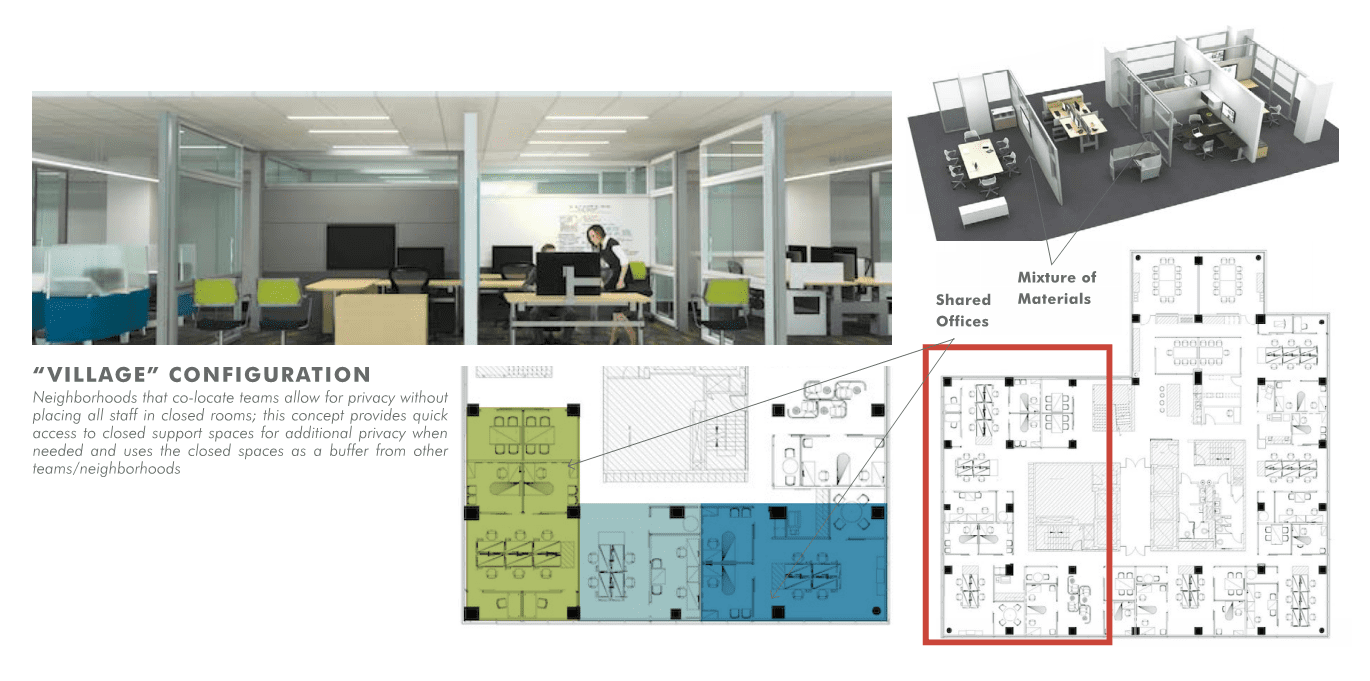
The “Village” Configuration
The second step in our visual confidentiality design methodology is to identify which user groups most often need to interact, yet have different (albeit comparable) levels of information access. In these cases, a physical barrier may be too disruptive to workflow to be practical. At the same time, a central meeting point is necessary, and shoulder surfing is a non-option.
To maximize collaboration between these disparate groups, IA relies on the “village” configuration to maintain separation. Relying on quantitative data collected by our workplace strategy team, IA is able to create neighborhoods of related work groups and maximize the use of closed support spaces. In this way, users are still able to work in a semi-open plan, but visual access to monitors (and therefore to passwords and other secure information) is severely limited.
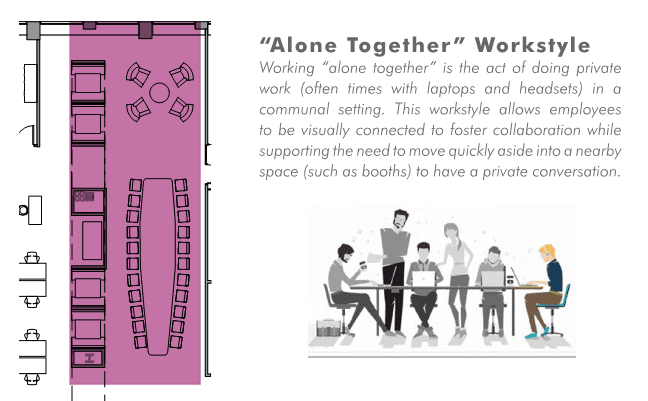
The “Alone Together” Workstyle
As collaboration increases and teams with different access have contact with each other, creating spaces where individuals can come together, yet step away at a moment’s notice to attend to a sensitive phone call, becomes necessary. These group workspaces serve the dual function of allowing an open office layout for employees with lower access to sensitive information yet provide usable huddle rooms ideal for processes where collaborators might be together for an extended amount of time.
Cloaking Technology
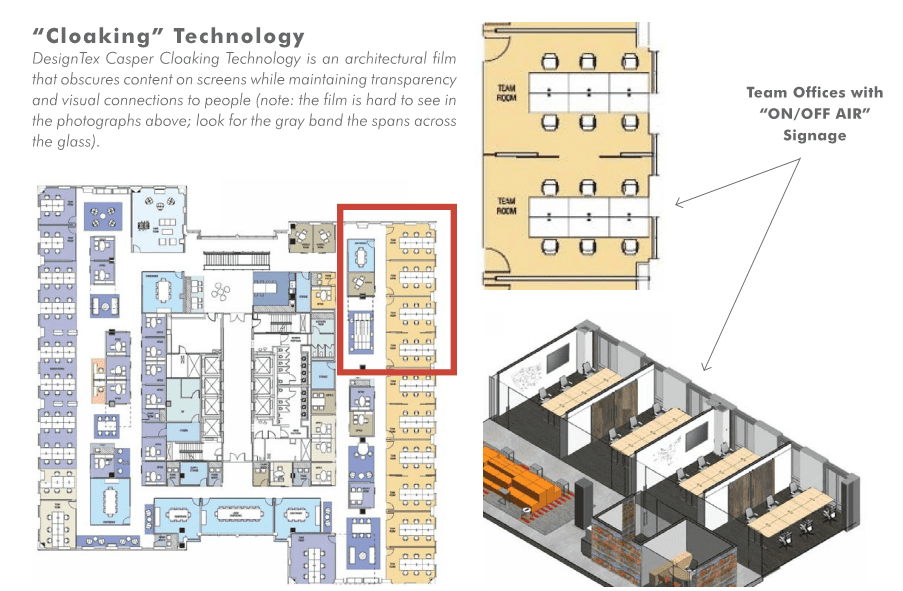
As we approach the “micro” level of collaboration and working groups become smaller, the next stage in the methodology may involve more direct visual interference in order to secure privacy. Where groups mentioned earlier weren’t necessarily collaborating on the same workflow, now employees are working together in small huddle rooms where sensitive information is being openly discussed. The utilization of cloaking technology can be applied directly to an individual (micro level) but is most commonly utilized for small group huddle rooms. Visual confidentiality is non-negotiable in this environment, but cannot inhibit the collaborative abilities of those using the huddle room.
In previous years IA would have relied on physical barriers such as walls, drapes, blinds, etc., to create a secure meeting environment. But as research continues to prove the positive impact of natural light on collaboration, creativity, and overall workplace performance, tactics are actively changing. Central to this is the utilization of cloaking technology, which functionally creates a two-way mirror for collaborative meeting spaces. Useful for centrally-located meeting areas, this film is applied to transparent structures in order to obscure any views into a given space. The film still allows almost 100% of existing daylight to enter the room, and a significant amount of light to exit the room, but what it doesn’t allow is for digital screens to be visible through the film. This means that group collaboration and presentation can go on unhindered in almost plain sight while maintaining a strict level of visual confidentiality.
Strategic Positioning
The most “micro” level of visual confidentiality management through design, Strategic Positioning, pertains to how employees work on an individual level, or in very small teams. Further mitigating any risk of shoulder surfing, collaboration areas are blocked off without significantly diminishing access to daylight or coworkers by utilizing well-placed furniture, lockers, decorative elements, and existing “closed” spaces. In such arrangements shoulder surfing is made all but impossible, precautions having been taken to maintain visual confidentiality in an open or semi-open office environment.
For one confidential software client in Virginia, this meant implementing confidential spaces for individuals in the form of high-backed, wrap-around chairs (pictured above middle), as well as at workstations.
Conclusion
As the largest global interior architecture and design firm, we’re able to monitor the various industries in which we provide our services, and to forecast security requirements for the future. Our advantage lies in sharing this information internally, adding and/or modifying these methodologies on a per project basis, and being ever-vigilant of how the principals of designing for confidentiality both impact each other and work together. As part one of a six- part series, we have considered visual confidentiality; in part two we will consider how acoustic confidentiality and open workspaces can coexist.
IA is a global firm of architects, designers, strategists, and specialists. We focus exclusively on environments through the lens of interior architecture—a radical idea in 1984, when IA was founded. We are highly connected agents of change, committed to creativity, innovation, growth, and community.
IA is a global firm of architects, designers, strategists, and specialists. We focus exclusively on environments through the lens of interior architecture—a radical idea in 1984, when IA was founded. We are highly connected agents of change, committed to creativity, innovation, growth, and community.